The holiday season presents an attractive opportunity for threat actors to exploit holiday travelers making reservations and travel arrangements. Threat actors continue to impersonate major brands, create fraudulent websites, employ social engineering tactics, and utilize artificial intelligence (AI) to produce convincing communications. They lure their targets through messages and phone calls, introducing fear or high-pressure tactics to encourage clicking on links or calling fake phone numbers in an attempt to steal personal data, financial information, account credentials, and funds.
Threat actors have registered over 4,300 domain names since the beginning of the year to create sophisticated phishing pages as part of an ongoing, massive phishing campaign . The registered domain names contain the impersonated business name and keywords (such as confirmation, booking, guestverify, guestcheck, cardverify, or reservation), followed by random numbers. Threat actors target potential travelers with malicious spam linked through the Want Your Feedback service, prompting them to click the link to visit the hotel’s website and confirm the reservation using a credit card. If clicked, the target is redirected through various websites before landing on a customized phishing page, which features logos from major online travel industry brands, such as Airbnb and Booking.com. Other customizations include translations into one of 43 languages, a fake CAPTCHA box, and a fraudulent online help chat. |
|
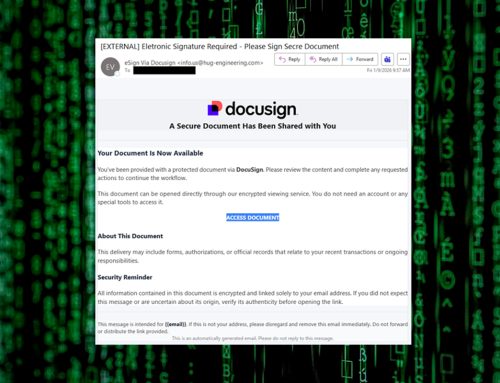
In a separate campaign, threat actors have conducted a sophisticated phishing operation targeting hotel customers globally. They use compromised email accounts to send malicious emails, purporting to be customer requests, to multiple hotel reservation and administration-related email addresses. The emails contain branding, include a malicious link, and employ the ClickFix social engineering tactic to compromise multiple booking platforms, such as Expedia and Booking[.]com, with infostealer malware to capture account credentials. |
|
|
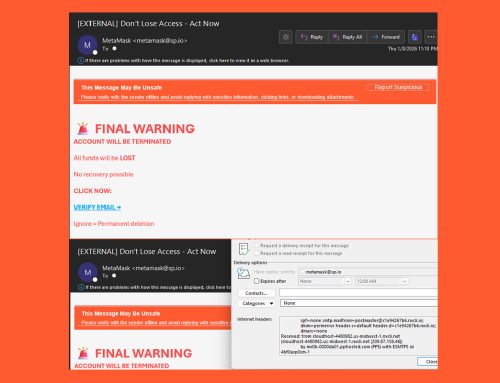
Threat actors then attempt to sell the stolen credentials on cybercrime forums or leverage them to send phishing emails or WhatsApp messages to hotel customers. The messages contain legitimate reservation details of the target, claim there was a security issue during the verification of the banking details, and then request confirmation of that information by visiting a phishing link. If the link is clicked, the target is directed to a phishing page that harvests the target’s banking information.
|
|
Threat actors may also exploit flight notifications, especially for delays or cancellations. For example, they may use real airline names, flight numbers, and logos to send fraudulent flight alerts through SMS text phishing. The official-looking alert aims to convince the target to react quickly without thinking. Threat actors trick their target into rebooking their flight by clicking the link or calling the airline’s customer service phone number. If the target clicks the malicious link or calls the fake phone number, the threat actors behind the scam claim to help rebook the flight for a fee but intend to steal their personal or financial information. Threat actors may also send fake confirmation emails to make the scam look legitimate and believable. |
|
A family lost more than $6,000 in a rebooking scam after booking flight reservations supposedly through a major airline, but never received seat assignments for one of their connecting flights. The victim received a message stating that there was a complication with their reservation, and called the airline’s phone number provided in the message. The victim thought they were speaking to an official airline representative who claimed that the airline would rebook the flights and issue a refund for the earlier reservations. The victim proceeded, but later learned that the phone number was not affiliated with the airline and that they would never receive the supposed refund. When the victim called the official airline’s phone number, they were informed that there was no call record and the original flight tickets had been purchased through a third-party website, rather than directly from the airline. |
|
- Refrain from clicking links and opening attachments from unknown senders.
- Exercise caution with unsolicited communications from known senders or legitimate platforms.
- Scrutinize messages, especially those with urgent language or confirmation of updates, changes, or requests.
- Confirm messages from senders by verifying their contact information obtained from trusted and official sources before taking action, such as clicking on links or opening attachments.
- Book accommodations only through known and trusted brands.
- Type official website URLs into browsers manually and only submit personal or financial information on official websites.
- Keep systems and browsers up to date.
- Consider using credit cards over debit cards, as they often have better consumer fraud protections.
- If victimized, contact your financial institution immediately, change passwords for the compromised account and any other accounts using the same password, and monitor accounts and statements for any unauthorized activity.
- Report malicious cyber activity to the NJCCIC and the FBI’s IC3.
|