By Malicious Invitation Only
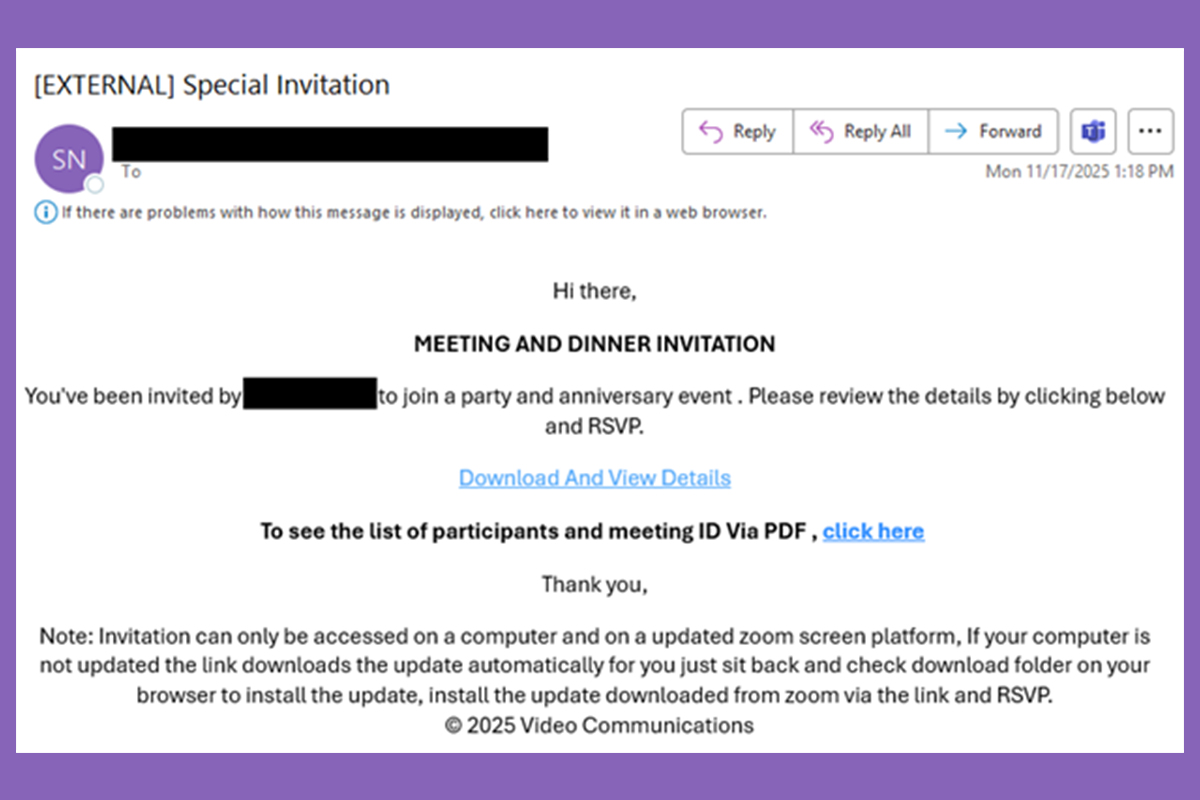
The NJCCIC observed a malware campaign leveraging social engineering, fake Zoom meeting invitations, and spoofed download websites. Threat actors compromised a user’s account and utilized their signature and organization branding to send emails purporting to be Zoom meeting and dinner invitations. The subject line displays “Special Invitation,” but the email is not personalized and uses improper grammar. The email contains links to convince the target to download and view details, including a participant list and the meeting ID.
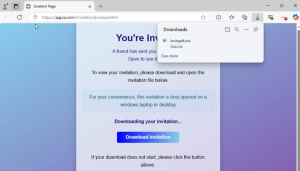
If one of the links is clicked, the target is directed to hxxps://zoommeetinginvlte[.]re
Recommendations
- Exercise caution with communications from known senders or legitimate platforms.
- Confirm requests from senders via contact information obtained from verified and official sources before taking action, such as clicking on links or opening attachments.
- Hover over links in emails or messages to view the actual destination URL before clicking.
- Be aware of homoglyph techniques in which threat actors exploit visually identical or similar characters from various fonts or alphabets.
- Type official website URLs into your browser manually and only submit sensitive information or download files from official websites.
- Keep systems and browsers up to date.
- Report malicious cyber activity to the NJCCIC and the FBI’s IC3.