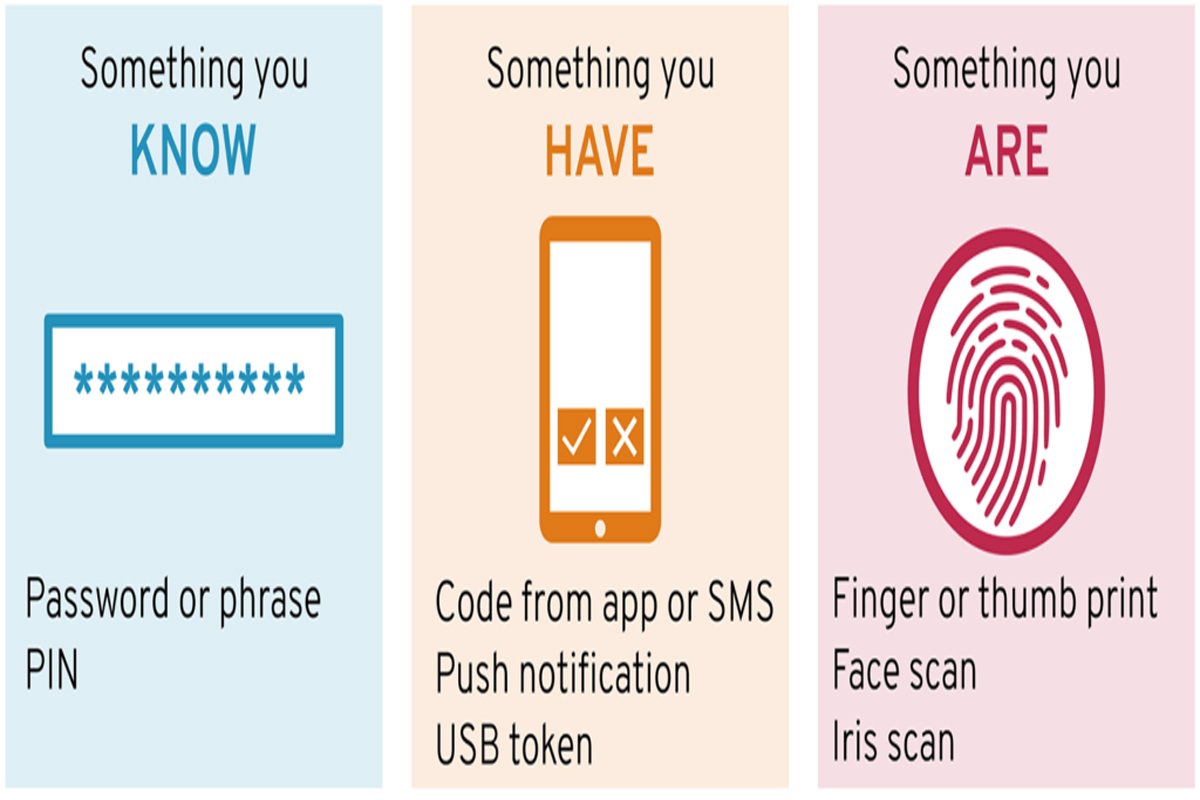
MFA: Why Do I Need This?
Authentication control is a process used to validate a user’s identity, and is accomplished by presenting a challenge to the user attempting to log into their account. This article explains how to implement MFA to help protect your online accounts from unauthorized access.