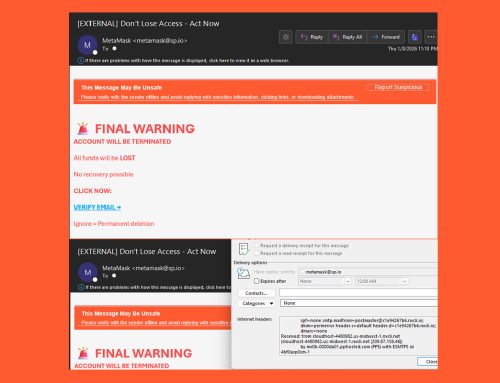
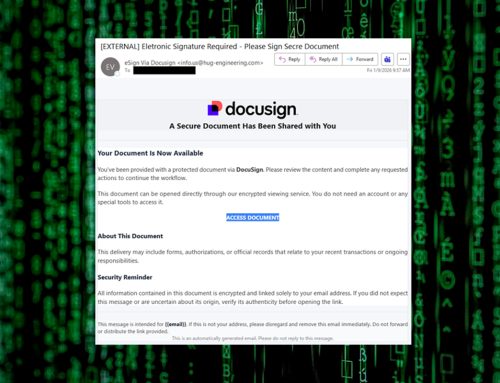
The NJCCIC identified a phishing campaign aimed at harvesting user credentials. The emails falsely claim that pending messages are waiting in the user’s organization mailbox and include a link to access them. Threat actors create a sense of urgency by warning that the messages might expire within 12 hours if not reviewed.
When clicking the “Access Your Messages” link, users are directed to a webmail phishing page that features the organization’s logo with the help of the ClearBit API. Any credentials entered in this form will be extracted and transmitted by bots to the threat actor’s Telegram account. |
|
- Avoid clicking links and opening attachments in unsolicited emails.
- Confirm requests from senders via contact information obtained from verified and official sources.
- Users should only submit account credentials on official websites.
- Maintain robust and up-to-date endpoint detection tools on every endpoint.
- Consider leveraging behavior-based detection tools rather than signature-based tools.
- If you suspect an account has been compromised, change the account’s password immediately and add a secondary authentication method.
- Report malicious cyber activity to the NJCCIC and the FBI’s IC3.
|