Look Both Ways Before Responding
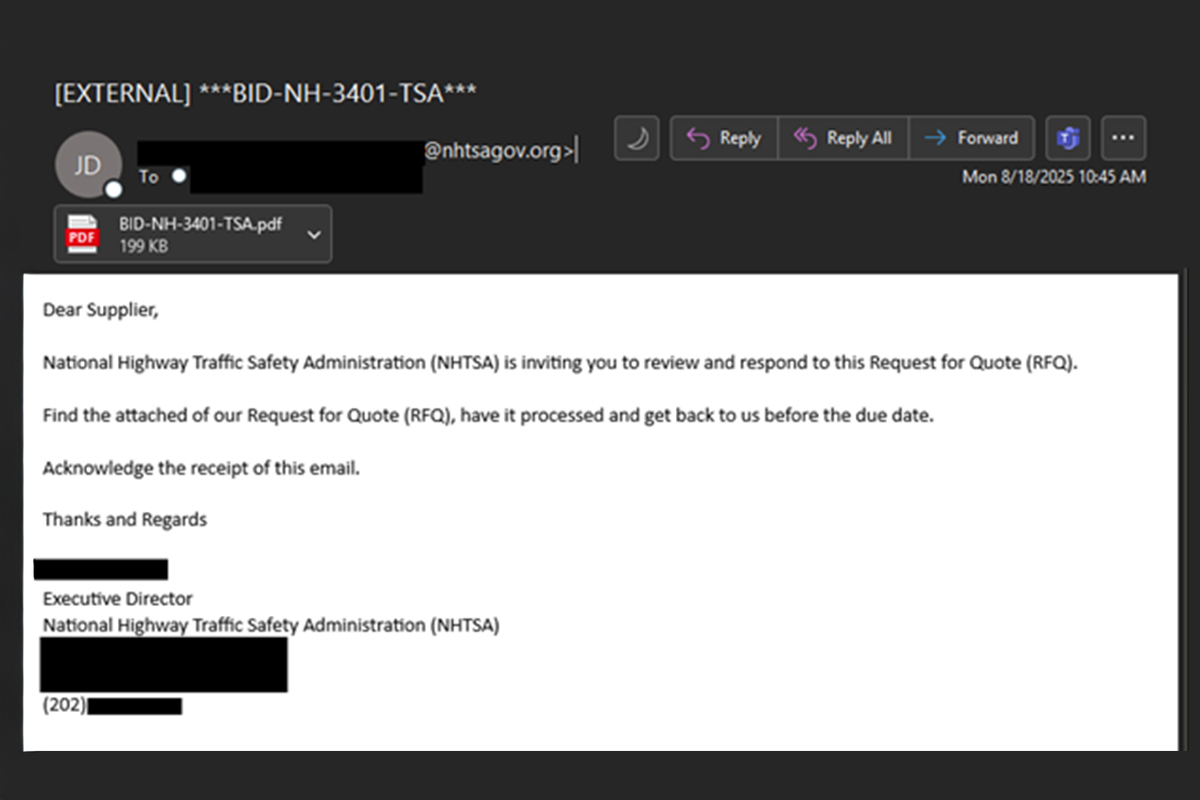
The NJCCIC observed a phishing campaign imitating the US National Highway Traffic Safety Administration. In this campaign, threat actors send a phishing email containing a PDF file that looks legitimate and appears to be benign. To add credibility to the email, the threat actors use nhtsagov[.]org as the email domain, an attempt to typosquat the true domain—nhtsa[.]gov.
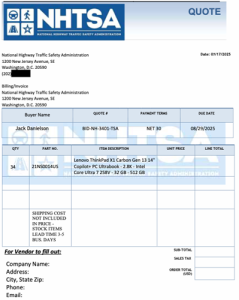
This type of social engineering attack resembles a Telephone-Oriented Attack Delivery (TOAD) campaign, where the true goal is to have a potential target contact the threat actors. If contacted, threat actors can exert further pressure to persuade the target to install a file, grant remote access, or inadvertently share credentials or personally identifiable information (PII).
Recommendations
- Facilitate user awareness training to include these types of phishing-based techniques.
- Refrain from responding to unsolicited communications, clicking links, or opening attachments from unknown senders.
- Confirm requests from senders via contact information obtained from verified and official sources.
- Keep systems up to date and apply patches after appropriate testing.
- Review the Don’t Take the Bait! Phishing and Other Social Engineering Attacks NJCCIC product for more information on common phishing and social engineering attacks.
- Report phishing and other malicious cyber activity to the NJCCIC and the FBI’s IC3.