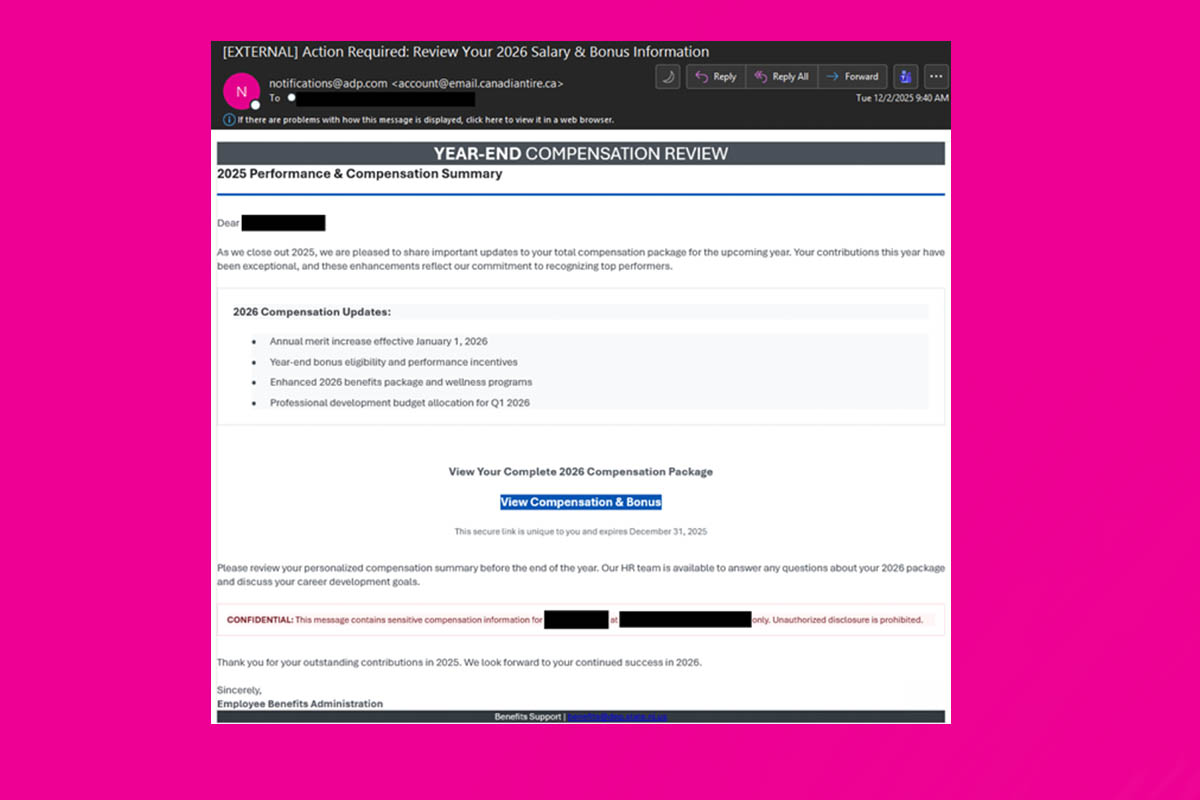
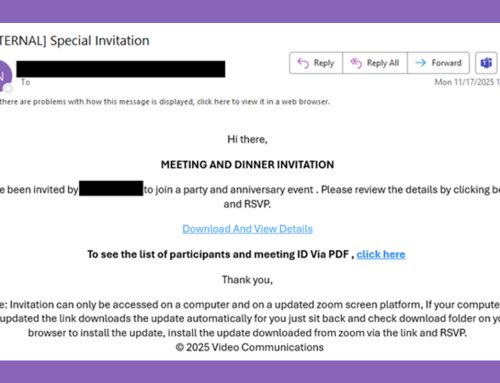
There has been an observed increase in campaigns that utilize timely and relevant bait to deceive users into downloading unknown files, remote monitoring and management (RMM) tools, and entering credentials on malicious websites. In these campaigns, threat actors pose as human resources (HR) departments and send emails claiming to contain information on upcoming salary increases and yearly bonuses. These lures include a deadline, adding a sense of urgency to reviewing the information, as well as a sense of excitement with the promise of monetary rewards.
These messages may include a file, a URL, or a QR code. In one version of this lure, users are directed to a page hosting a CAPTCHA that, when solved, leads users to a fake Google Authentication page. Credentials, along with 2FA tokens and associated session cookies, are captured in real-time using the Adversary-in-the-Middle (AiTM) technique, leveraging synchronous relay capabilities provided by the Tycoon Phishkit. |
|
|
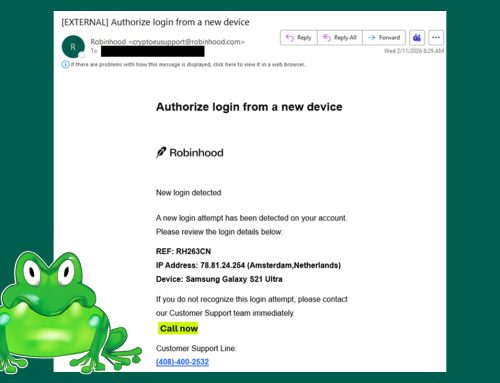
In another version of this lure, messages contain a URL utilizing Cloudflare for IP filtering and if passed, redirects to a counterfeit Microsoft authentication page. After the user submits an email address, the page displays the organization's Azure Active Directory (ADD) or Okta branding and captures user credentials, 2FA tokens, and session cookies through an AiTM synchronous relay.
|
|
- Avoid clicking links and opening attachments in unsolicited emails.
- Confirm requests from senders via contact information obtained from verified and official sources.
- Users should only submit account credentials on official websites.
- Maintain robust and up-to-date endpoint detection tools on every endpoint.
- Consider leveraging behavior-based detection tools rather than signature-based tools.
- If you suspect an account has been compromised, change the account's password immediately and add a secondary authentication method.
- Review the Don't Take the Bait! Phishing and Other Social Engineering Attacks NJCCIC product for more information on common phishing and social engineering attacks.
- Report malicious cyber activity to the NJCCIC and the FBI's IC3.
|