Cyber Command
Cyber Command Corporation is an IRS approved 501(c)(3) nonprofit, public charity that offers cybersecurity awareness training and develops viable cybersecurity defense software.
Mission Statement
Cybersecurity concerns are one of the most critical threats facing the security of our nation, which impacts all United States citizens, including individuals, families, businesses of all sizes and verticals, and government organizations.
Our mission is to reduce threat risk by promoting cybersecurity education and awareness, facilitating research, advancing development, and enabling dissemination of cybersecurity defense products and services to USA individuals, public and private organizations.
Want to organize a free virtual or in-person cybersecurity class for seniors in your neighborhood? Please contact us below and we’ll get the process started!
Cybersecurity Intelligence Feed & Resources
This section contains free cybersecurity related articles and knowledge to help learn critical cybersecurity lessons.
Vulnerabilities in Ivanti Endpoint Manager
Multiple vulnerabilities have been discovered in Ivanti Endpoint Manager, the most severe of which could allow for authentication bypass. Ivanti Endpoint Manager is a client-based unified endpoint management software. uccessful exploitation of the most severe of these vulnerabilities...
Vulnerabilities in Ivanti Endpoint Manager
Multiple vulnerabilities have been discovered in Ivanti Endpoint Manager Mobile which could allow for remote code execution. Ivanti Endpoint Manager Mobile is a mobile management software engine that enables IT to set policies for mobile devices, applications and content.
Vulnerability in Microsoft Office
A vulnerability has been discovered in Microsoft Office which could allow for a security feature bypass. Microsoft Office is a suite of applications designed to help with productivity and completing common tasks on a computer. Microsoft reports CVE-2026-21509 was exploited in the wild.
Payroll Phishing Campaign
The NJCCIC received multiple reports of a payroll phishing campaign targeting New Jersey school districts. The subject line references a payroll increment project or direct deposit notice. Threat actors impersonate the superintendent or an administrator by compromising their account.
Toll Wars: Return of the SMiSh
The NJCCIC received a new wave of reports of SMS text phishing (SMiShing) scams impersonating the New Jersey Motor Vehicle Commission (MVC). These urgent-sounding messages claim to be a final notice about an unpaid traffic violation, with a short deadline to...
Monroe University Data Breach
Monroe University disclosed a data breach affecting over 320,000 people. Threat actors gained unauthorized access to computer systems for two weeks in December 2024 and acquired copies of some files. A review of the files revealed stolen personal, financial, and health information.
Salt Typhoon Targets US House Committee
Salt Typhoon is believed to be behind a recently disclosed cyber espionage campaign targeting US House committees and staff. In December 2025, researchers identified intrusions that compromised email systems within the US House of Representatives.
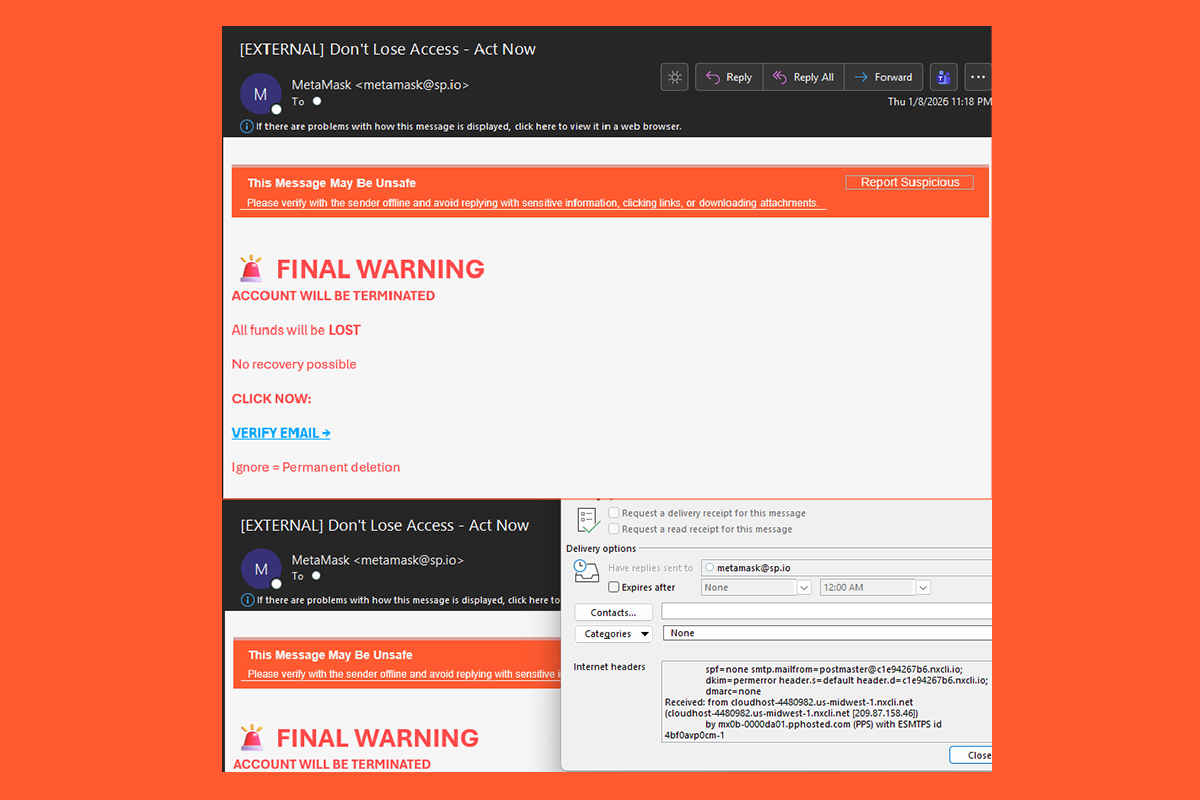
Phishing for Crypto Campaign
The NJCCIC observed a phishing campaign targeting MetaMask cryptocurrency wallets. The message appears to come from MetaMask, but the actual originating email address can be found in the header information. The threat actor also uses Punycode in the "From" field...
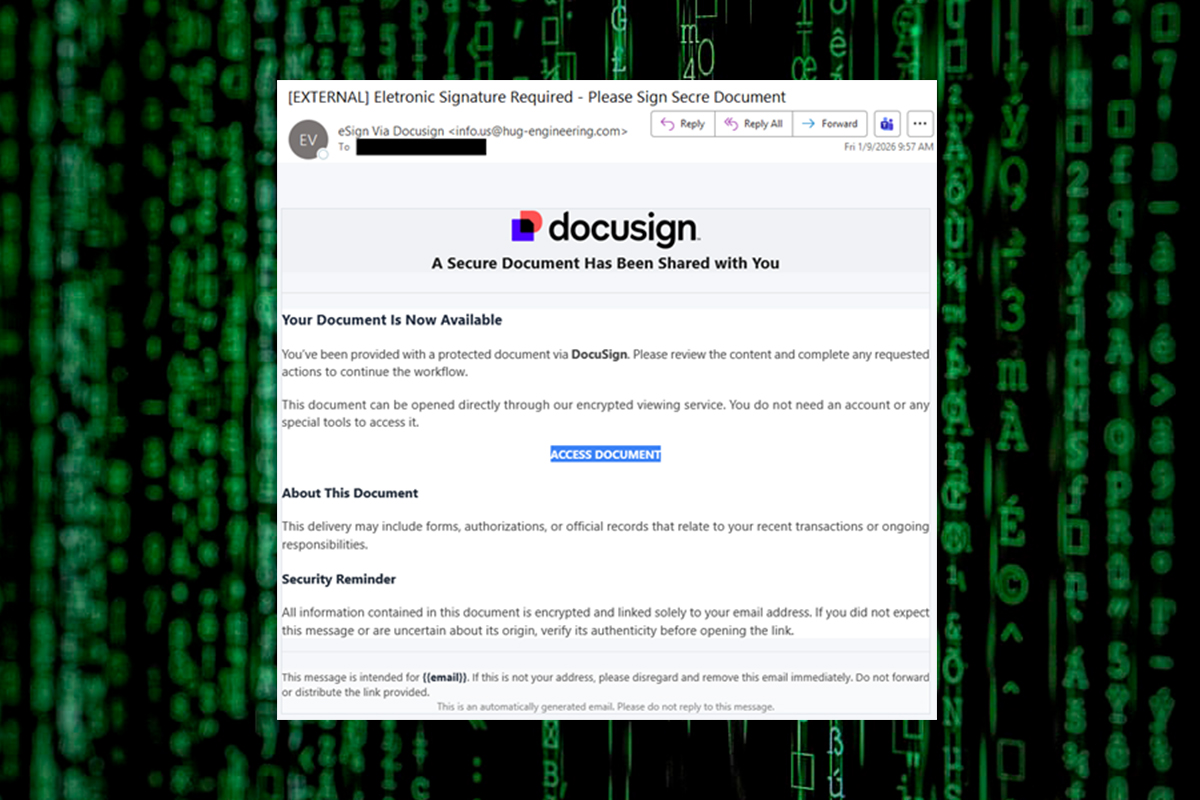
Docusign Phishing Installs LogMeIn
The NJCCIC observed a phishing campaign that abused the legitimate Docusign, leading to the installation of the LogMeIn Resolve remote monitoring and management (RMM) tool. The email is not sent from a legitimate Docusign domain, such as docusign[.]com or docusign[.]net.
Our Services
C3 helps reduce the risk of compromise by promoting cybersecurity education and awareness, and by facilitating research, development and dissemination of viable cybersecurity defense products and services to individuals, public and private organizations in the United States.
In-Person Training Classes
Virtual Classes
Phishing Simulations
Security Posture Analysis
Credential Leak Checks
Policies, Procedures & Plans
Phishing Attack Prevention
Network Intrusion Protection
Actionable Intelligence
Cyber Command is a registered 501(c)(3) nonprofit, public charity. EIN 93-2718000.
Our Board of Directors

Joshua Weiss, President

Arthur Warady, Treasurer

Kelly Whitis, Secretary
Contact Us
We’d love to hear from you. Please use the contact form below to reach us.