Phishing: Detection Evasion Tactics
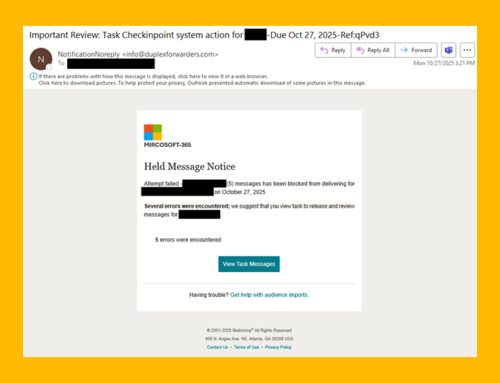
The NJCCIC identified a phishing campaign that uses tactics to make detection more difficult, leading to increased account compromises.
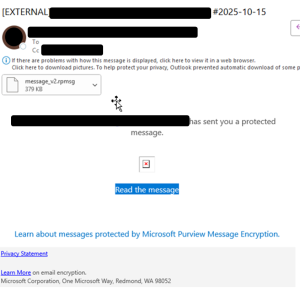
Users receive an initial encrypted email with an encrypted link to “Read the message,” which leads to a legitimate Microsoft 365 login page with the URL beginning with “hxxps://outlook.office365[.]
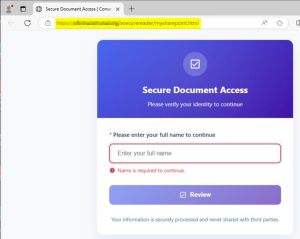
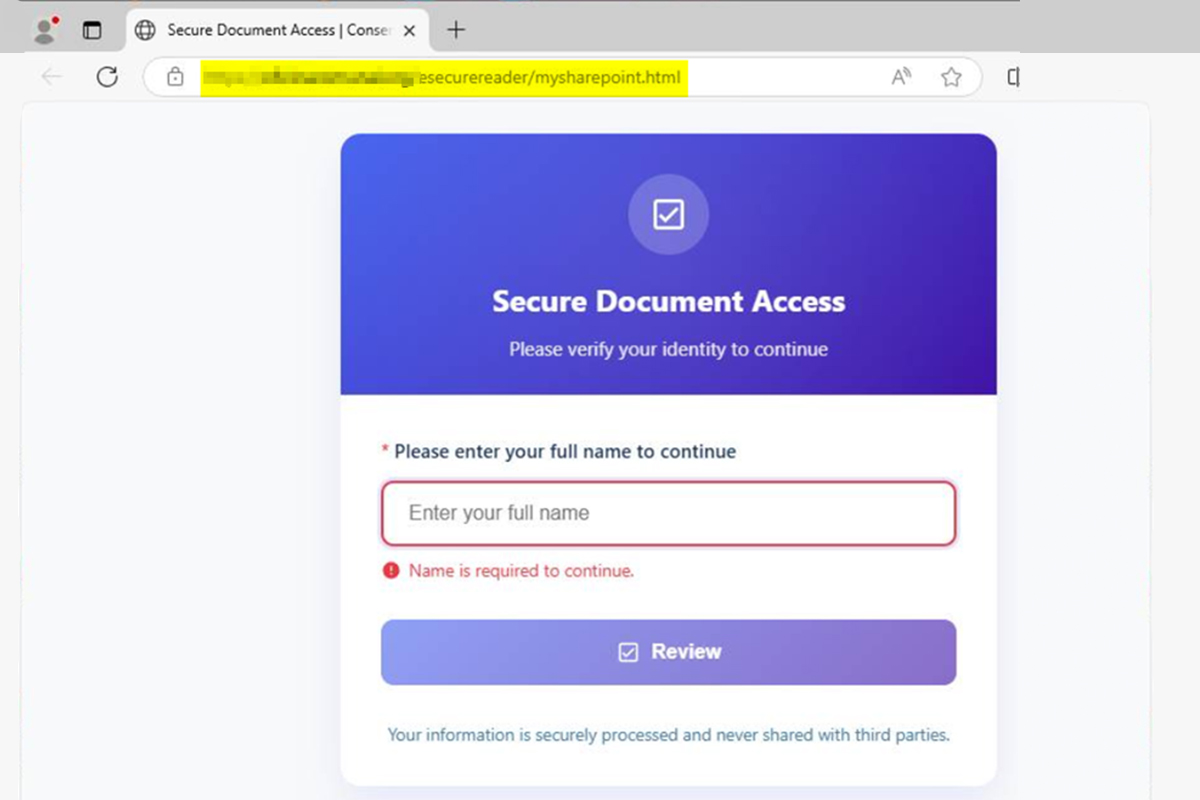
Once login credentials are submitted, the user is directed to a webpage titled “Secure Document Access” with a URL ending in “mysharepoint[.]html.” This webpage requests the user to verify their identity to continue, beginning with their full name.
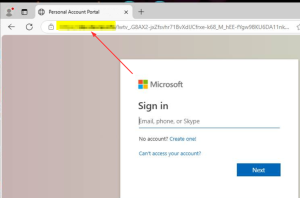
They are then redirected to a fraudulent Microsoft 365 login page to submit their credentials again. This time, if the credentials are submitted, they are stolen by the threat actor behind the scheme and used to compromise the user’s account and target their contacts to perpetuate the phishing campaign. The webpage URLs used in this campaign are personalized to include the recipient’s email address in order to convey legitimacy.
Recommendations
- Exercise caution with all communications, even those from known contacts, and refrain from clicking links, opening attachments, or providing sensitive information to a user unless their request is determined legitimate by contacting them via a separate means of communication.
- Type official website URLs into browsers manually and only submit sensitive information on official websites.
- Notify users of this and similar tactics to increase awareness and reduce the risk of account compromises.
- If an account is compromised, the NJCCIC advises the following:
- Immediately reset the user’s password and revoke session tokens from the compromised account.
- Enable multi-factor authentication (MFA), choosing authentication apps or hardware tokens over SMS- or email-based codes whenever possible.
- Notify the user’s contacts of the compromise, advising them not to click on links, open attachments, or provide information in response to messages sent from the compromised account.
- Monitor for suspicious and anomalous account and network activity.