There’s a RAT Hiding in This Email
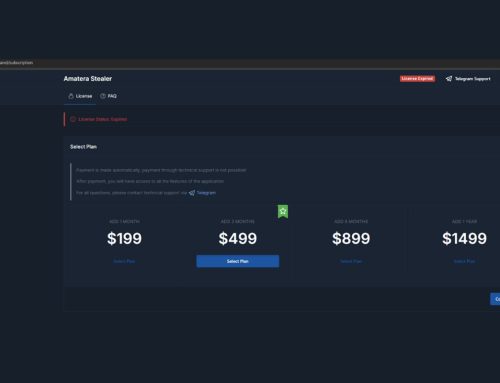
The NJCCIC observed a campaign attempting to distribute Agent Tesla malware. Agent Tesla functions as a remote access trojan (RAT) with information-stealing capabilities, including keystroke logging, password harvesting, clipboard theft, and screen capture. While first discovered in 2014, Agent Tesla remains a popular Malware-as-a-Service (MaaS).

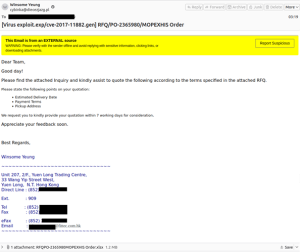
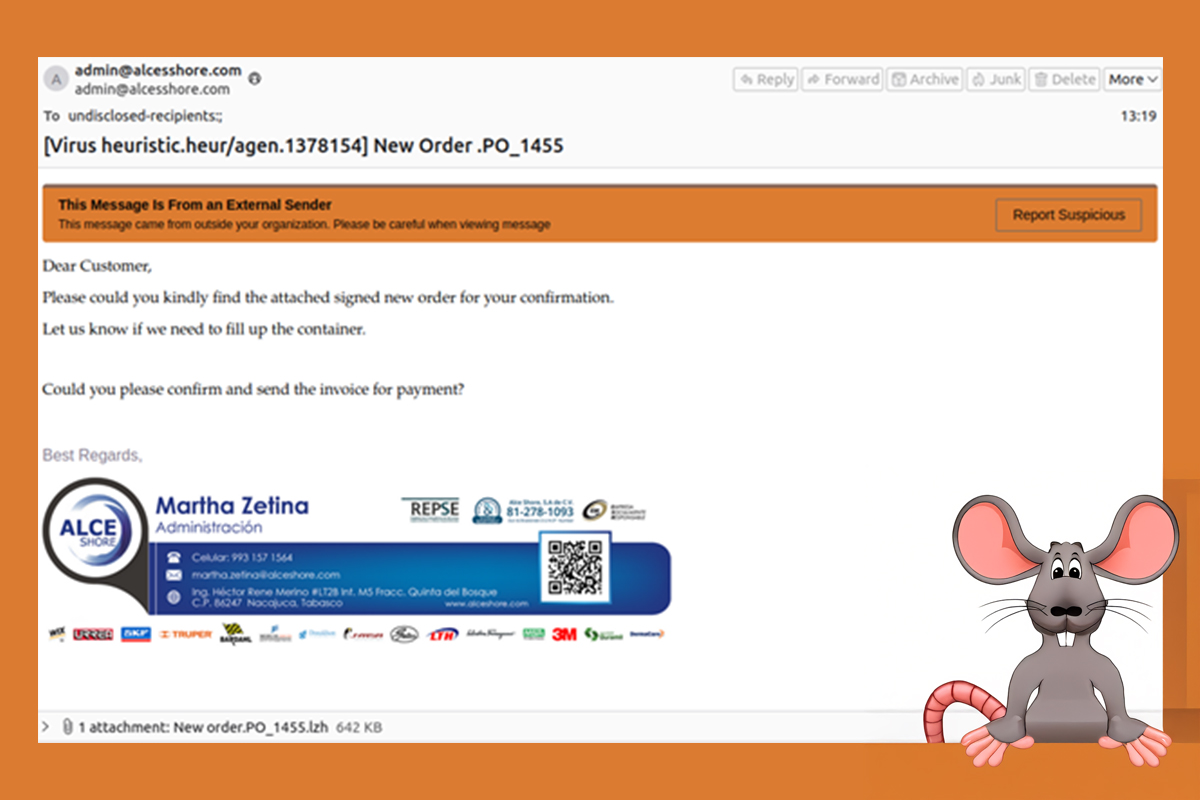
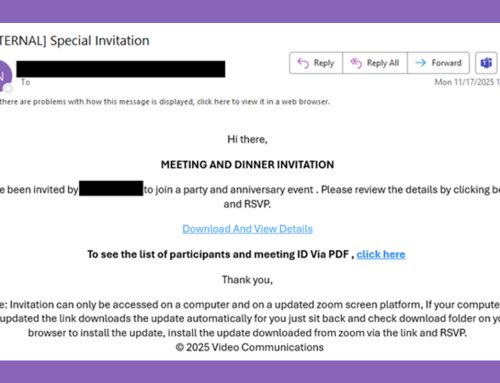
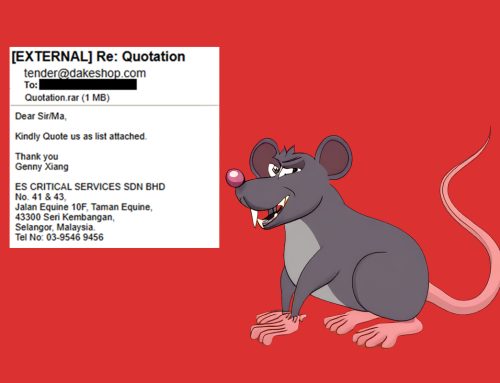
In this campaign, threat actors send phishing emails claiming to include order forms, invoices, or other similar financial documents. These messages include either a compressed executable file or a Microsoft Excel attachment that exploits vulnerabilities in Equation Editor. When opened, these attachments will download and install Agent Tesla.
Recommendations
- Avoid clicking links and opening attachments in unsolicited emails.
- Confirm requests from senders via contact information obtained from verified and official sources.
- Only download applications and software from official sources.
- Maintain robust and up-to-date endpoint detection tools on every endpoint.
- Consider leveraging behavior-based detection tools rather than signature-based tools.
- If you suspect an account has been compromised, change the account’s password immediately and ensure multi-factor authentication (MFA) is enabled for all online accounts.
- Review the Don’t Take the Bait! Phishing and Other Social Engineering Attacks NJCCIC product for more information on common phishing and social engineering attacks.
- Report malicious cyber activity to the NJCCIC and the FBI’s IC3.