These Emails Are Best Left in Quarantine
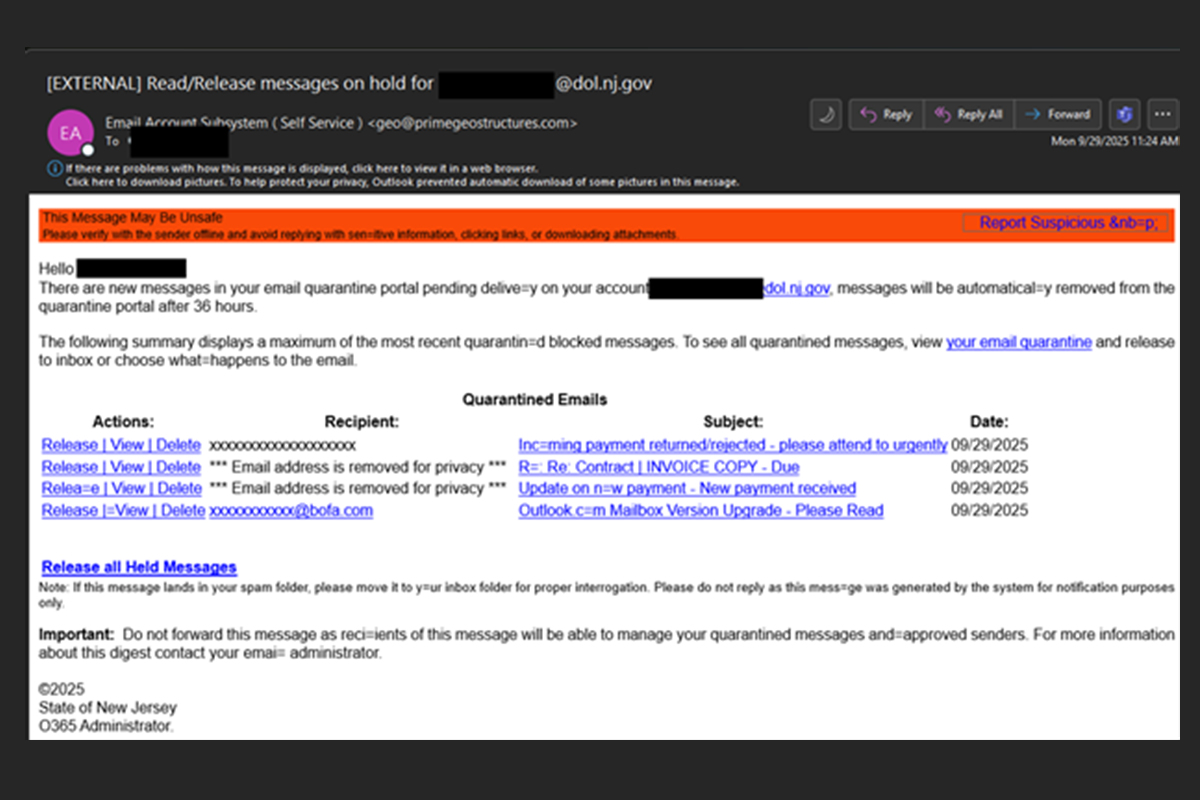
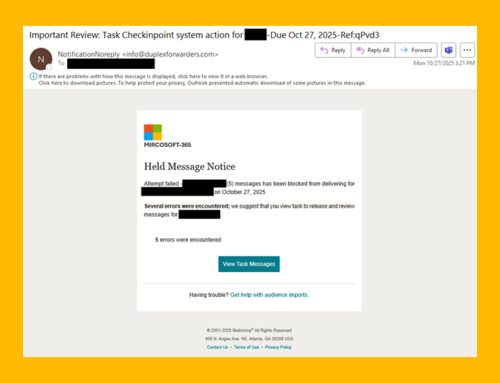
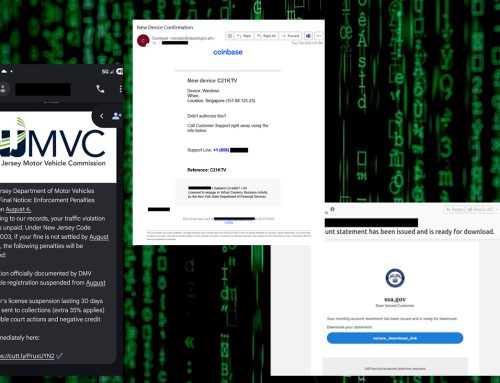
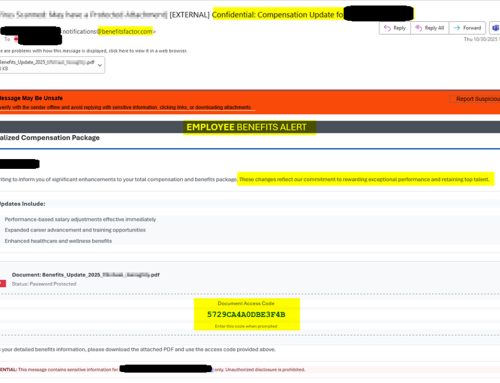
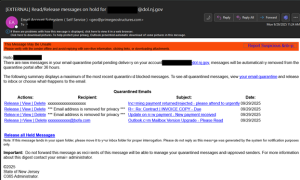
TThe NJCCIC has observed a phishing campaign posing as an automated notification about quarantined emails. Many companies employ email security protection, which often includes a quarantine feature that holds potentially risky emails for user review.
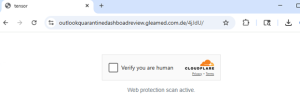
If a user clicks on one of the provided links, a CAPTCHA page will load, requiring the user to verify before they can proceed. These pages are often utilized in phishing scams because they can prevent email security systems from detecting the malicious nature of the emails.
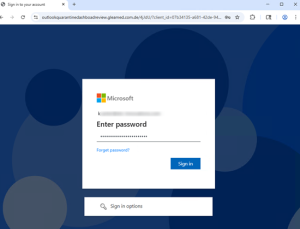
Once verified, a page that appears to be a legitimate Microsoft login page loads; however, the URL is a warning sign that this is not a genuine Microsoft page. Any credentials entered will be harvested through synchronous relay capabilities, a technique known as an Adversary-in-the-Middle (AiTM) attack. Associated session cookies will also be collected. Researchers have discovered that the threat actor behind this campaign is using the ODx Phishing-as-a-Service (PhaaS) kit, also tracked as Storm-1167.
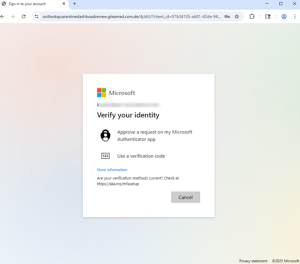
Finally, the target will receive a request for approval from the Microsoft Authenticator. Although the request may seem legitimate, approving it will grant the threat actors access to the target’s account.
Recommendations
- Avoid clicking links and opening attachments in unsolicited emails.
- Confirm requests from senders via contact information obtained from verified and official sources.
- Users should only submit account credentials on official websites.
- Maintain robust and up-to-date endpoint detection tools on every endpoint.
- Consider leveraging behavior-based detection tools rather than signature-based tools.
- If you suspect an account has been compromised, change the account’s password immediately and add a secondary authentication method.
- Report other malicious cyber activity to the NJCCIC and the FBI’s IC3.