Threat Actors Steal More Than Romance
The NJCCIC continues to receive reports of romance scams targeting New Jersey residents to steal funds. Threat actors typically create fake accounts on social media platforms or dating apps to pose as potential new friends or love interests. They increasingly use artificial intelligence (AI) technologies to disguise their voice and face. They may strategically target vulnerable populations , such as widowed or divorced older adults, who typically have more assets or money. Once the threat actors contact their targets through direct messages, video chats, emails, or text messages, they pretend to express genuine interest and establish trust before asking for information or funds. While some reports indicated romance scam attempts with no reported losses, other victims reported losses ranging from several hundred to several thousand dollars.
Threat actors may use emotional stories to gain sympathy and compassion and request money for supposed emergencies, medical bills, etc. In one scam, the threat actor claimed to be a refugee seeking asylum in the US. They scammed their victim into paying around $35,000 in expenses to cover supposed legal fees, deportation costs, rent payments, family medical bills, and funeral expenses. In another scam, the threat actor purported to be an astronaut in distress and under attack in space. They scammed their older adult victim into paying around $6,700 for life-saving oxygen.
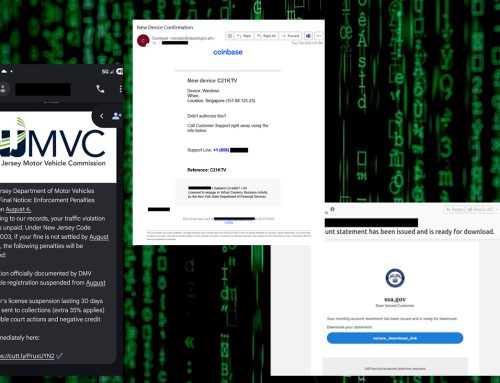
Threat actors increasingly use romance scams to build trust and introduce their targets to fake investment opportunities, including pig butchering schemes in cryptocurrency scams . They may use pressure tactics, false promises of high returns, fake testimonials, or evidence to convince their target to invest. In one scam, threat actors claimed to have called the wrong phone number and supposedly developed a romantic online relationship with their target. After establishing trust, they convinced their target to invest money with a high return, as evidenced by the provided statements. They further advised the target to invest additional money on a timely basis or risk being penalized. After making several payments, the threat actors claimed they were compromised and needed the target to resend a similar payment. Once paid, all communications ceased, and the money invested of approximately $250,000 was lost.
Threat actors also socially engineer their targets’ heartstrings to extort funds through fake business investment opportunities. In one report, they communicated with their target through a dating app and presented an opportunity to invest in a purported online store. They agreed to open the online store together and deposit money to cover costs. As orders were fulfilled, the target deposited additional funds to account for future orders, including larger ones. When the target wanted to meet in person, the threat actors gave them a fake physical address, and the $50,000 investment was lost.
Similar to romance scams, threat actors create fake accounts, pose as potential love interests, and build trust in sextortion scams before requesting or offering to exchange explicit material. If the target sends explicit material, the threat actors threaten to publish or share it with the target’s friends and family. If the target refuses, threat actors can also use non-explicit content posted on the target’s social media page or dating app to create AI-generated, realistic, explicit content. They can extort their victims in a matter of minutes and often harass them to make additional payments.
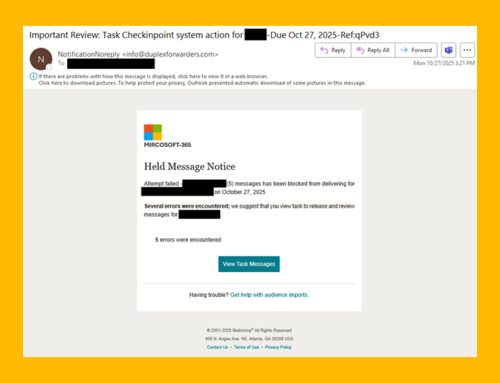
Threat actors also continue to target and steal funds from unsuspecting potential victims in the classic sextortion scam by claiming to have obtained explicit content. Threat actors typically email their targets, purporting to have successfully compromised the target’s system via malware or spyware, such as Pegasus software. They also claim that they have secretly recorded webcam footage of their inappropriate online behavior while watching pornography. They threaten to release the compromising or sexually explicit images or videos of the target to contacts or social media platforms if payment is not made. They may also threaten to physically harm the target or loved ones to ensure payment is made. In most cases, these threats are not credible, as threat actors cannot provide proof of compromise or authentic content. Therefore, users are advised to disregard these emails and refrain from sending funds.
Unlike the claims of malware and obtained content in the classic sextortion scam, threat actors are leveraging malware with automated sextortion features. The open-source Stealerium infostealer not only can infect systems through malicious emails and steal sensitive data like other infostealers, but it is also an automated tool capable of actively monitoring browsing habits for pornography-related data. Once adult content-related open browser tabs are detected in real time, it discreetly activates the target’s webcam without illuminating the indicator light. It simultaneously takes desktop screenshots and captures webcam images. Once captured, the data is exfiltrated to the threat actors in the background and most likely used in extortion attempts. Since May 2025, Stealerium has increased in usage and could lead to an uptick in sextortion scams.
The NJCCIC continues to receive reports of sextortion scams from New Jersey residents to steal funds. Although most reports indicated sextortion attempts with no reported losses, some victims reported losses ranging from $200 to $1,000 via Bitcoin, Venmo, CashApp, or gift cards. The US Department of the Treasury’s Financial Crimes Enforcement Network (FinCEN) issued a notice to help financial institutions identify red flags and detect suspicious activity associated with financially motivated sextortion schemes. The notice also highlights the importance of reporting activity to law enforcement to disrupt the threat actors and help prevent further victimization.
Recommendations
- Reduce your digital footprint so threat actors cannot easily target you.
- Refrain from responding to unsolicited communications, clicking links, or opening attachments from unknown or untrusted senders. Exercise caution with communications from known senders.
- Independently verify unsolicited requests or offers and do not release any personally identifying information, financial details, or funds until you have confirmed their legitimacy.
- Review security and privacy settings for accounts, social media platforms, browsers, and devices regularly, including cameras and microphones.
- Cover webcams with a webcam cover or physical tape to help prevent malware from capturing you or sensitive data if it takes control of your camera.
- Refrain from sending explicit content of yourself to an unknown party. If you already have, do not send funds and immediately block them from all communications or platforms.
- Report malicious cyber activity to the NJCCIC, the FBI’s IC3, and the FTC.
- If you or someone you know is being physically threatened, contact your local police department or dial 9-1-1 immediately.