Threat Actors Want Your Remote…Access
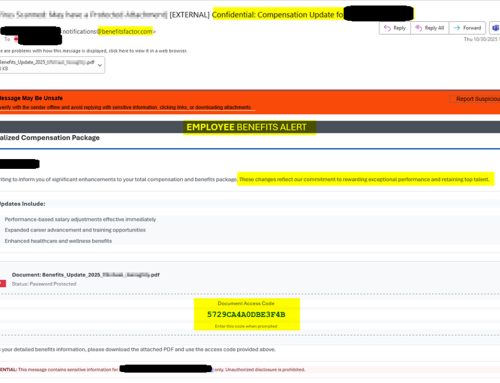
The NJCCIC has observed threat actors continuing to exploit remote monitoring and management (RMM) tools such as PDQ Connect, ScreenConnect, ITarian, and Atera to remotely access target environments. The use of RMM software enables threat actors to gain initial access, often without triggering security alerts due to the legitimate nature of these programs. Once installed, RMM tools can be used similarly to remote access trojans (RATs), enabling threat actors to exfiltrate data, maintain persistent access, move laterally, and even download malware.
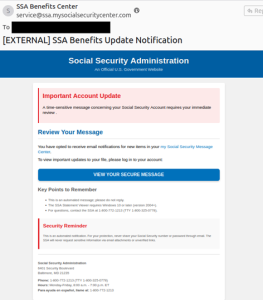
The NJCCIC has observed threat actors continuing to exploit remote monitoring and management (RMM) tools such as PDQ Connect, ScreenConnect, ITarian, and Atera to remotely access target environments. The use of RMM software enables threat actors to gain initial access, often without triggering security alerts due to the legitimate nature of these programs. Once installed, RMM tools can be used similarly to remote access trojans (RATs), enabling threat actors to exfiltrate data, maintain persistent access, move laterally, and even download malware.
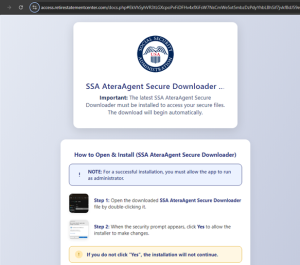
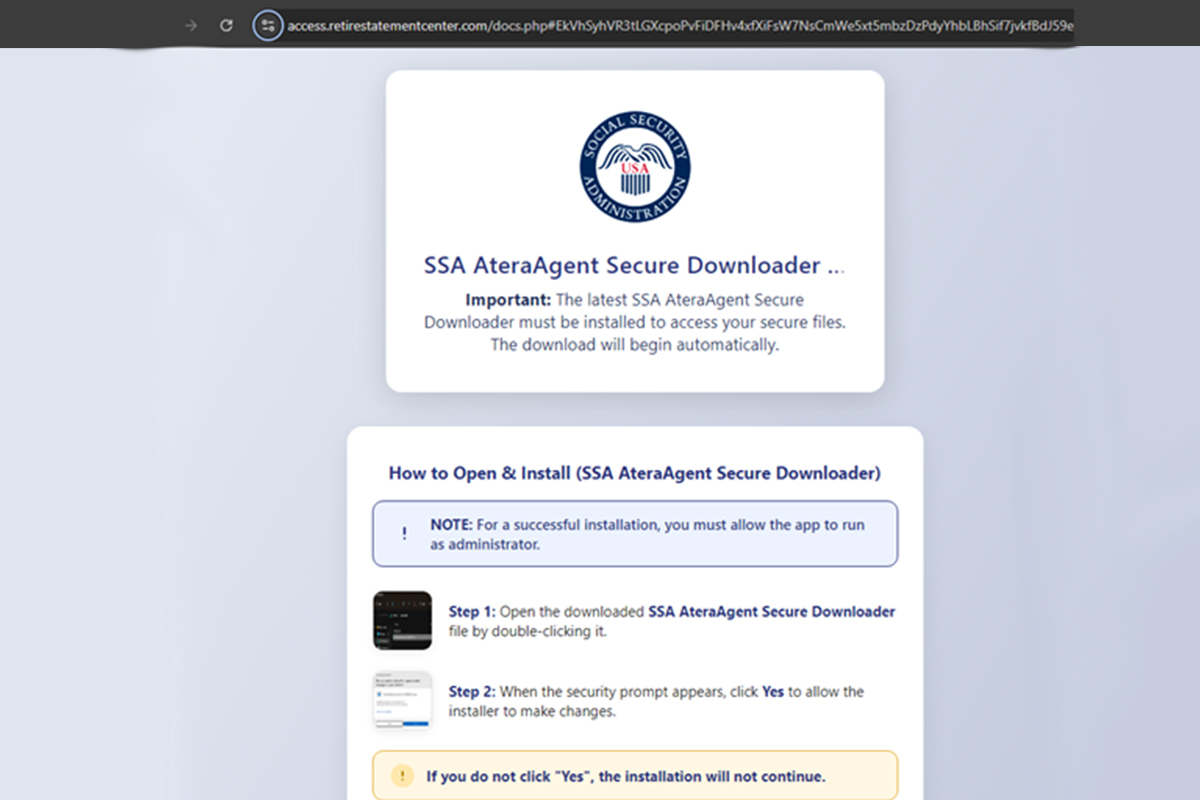
Upon clicking the URL in the phishing email, users are directed to a website with instructions that claim certain software must be installed before they can access their secure files. After installing the software and running it as an administrator, threat actors can gain full remote control of the victim’s system. The NJCCIC has also recently reported on campaigns distributing PDQ Connect, Microsoft Quick Assist , and ScreenConnect.
Recommendations
- Facilitate user awareness training to include these types of phishing-based techniques.
- Block remote access tools except those used by the organization for legitimate uses.
- Refrain from responding to unsolicited communications, clicking links, or opening attachments from unknown senders.
- Confirm requests from senders via contact information obtained from verified and official sources.
- Keep systems up to date and apply patches after appropriate testing.
- Review the Don’t Take the Bait! Phishing and Other Social Engineering Attacks NJCCIC product for more information on common phishing and social engineering attacks.
- Report phishing and other malicious cyber activity to the NJCCIC and the FBI’s IC3.