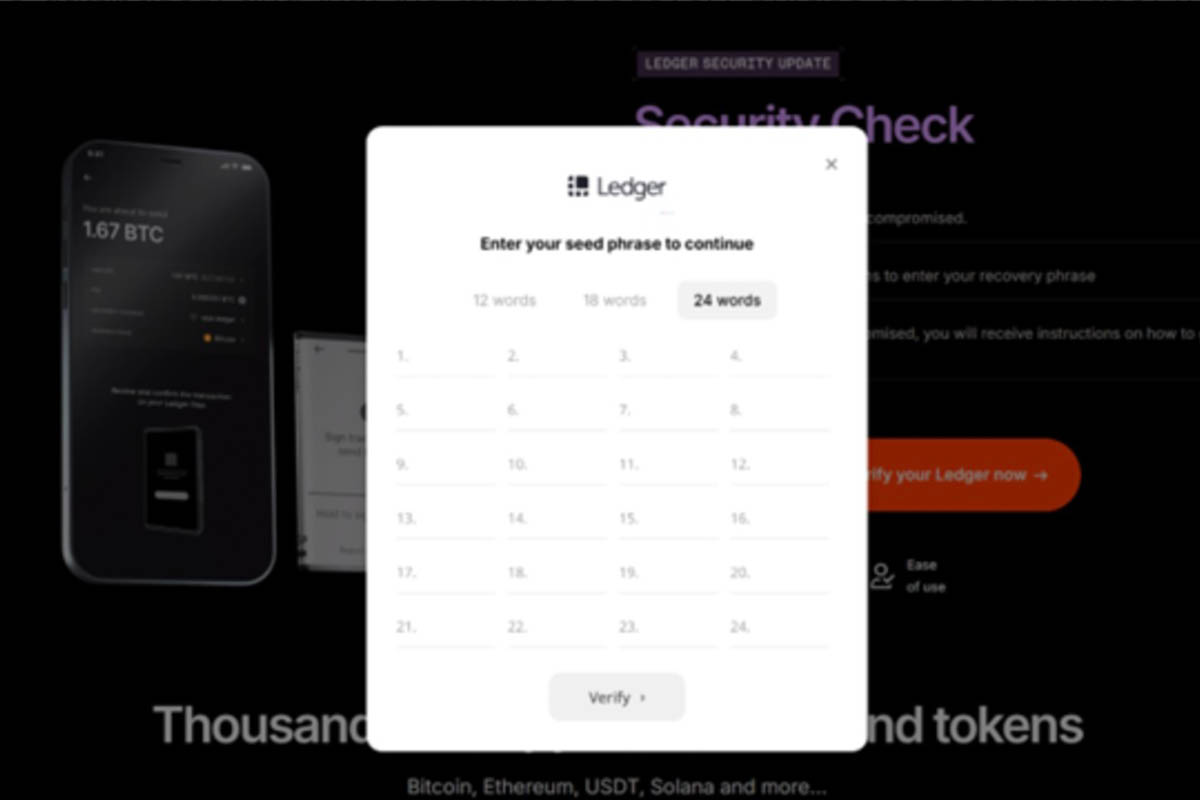
T\he NJCCIC observed a Ledger-themed cryptocurrency drainer phishing campaign targeting New Jersey State employees. Although “Ledger” appears in the sender’s display name, the sender’s email address does not reference Ledger and comes from a “.kr” top-level domain (TLD) for South Korea. The emails are sent via SendGrid, which provides high deliverability, tracking, and analytics for transactional emails, such as notifications. Threat actors impersonate Ledger Support, claiming to have identified unauthorized access to one of their sensitive databases, and that the target’s recovery phrase (or seed phrase) may have been exposed. To ensure funds remain secure, they request the target to verify whether their recovery phrase has been compromised using an encrypted verification portal
| The messages contain a “Verify My Recovery Phrase” link (hxxps://ozekfok[.]s3[.]eu-north-1[.]amazonaws[.]com/oke[.]html) directing the target to a Ledger phishing page (hxxps://portal-sign-ledger[.]com). If the “Verify your Ledger now” button is clicked, the target is prompted to enter their 24-word recovery phrase. If submitted, threat actors have full access and control of the associated cryptocurrency wallet. They can then transfer funds to a wallet under their own control, resulting in a total loss for the target. |
|
Ledger provides additional information and recommendations for ongoing phishing campaigns targeting users through physical mail, phone calls, fake versions of the Ledger Wallet application or website, fake emails, scam NFTs, and fake social media accounts. Ledger or someone from Ledger Support will never ask users for their 24-word recovery phrase. |
|
- Avoid clicking links, opening attachments, responding to, or acting on unsolicited communications.
- Confirm messages from senders by verifying their contact information obtained from trusted and official sources before taking action, such as clicking on links or opening attachments.
- Type official website URLs into browsers manually and only submit account credentials, personal information, or financial details on official websites.
- Always refrain from sharing your private key, seed phrase, or secret recovery phrase with anyone.
- Keep systems and apps up to date.
- Report these scams and malicious cyber activity to the NJCCIC, the FBI’s IC3, and the FTC.
- If victimized, monitor bank accounts, credit profiles, and other online accounts for irregularities or suspicious activity.
- Review the Identity Theft and Compromised PII NJCCIC Informational Report for additional recommendations and resources, including credit freezes and enabling MFA on accounts.
- Review the NJCCIC Cryptocurrency Scams webpage for additional information, recommendations, and resources.
|